Strategy
National Strategic Assessment 2020
This report sets out our latest assessment of the issues we face and the risks that gambling poses to consumers and the public
The person gambling - Engaged gamblers who participate in multiple products across different providers
A challenge to addressing the person-centric risk to the licensing objectives is the ability for consumers to circumvent any individual operator-led controls by gambling with several different companies. This is not an impediment to progress on controls to address the risk in those scenarios where significant markers of harm, criminal spend, or suspicious activity is confined to activity with a single licensee or group.
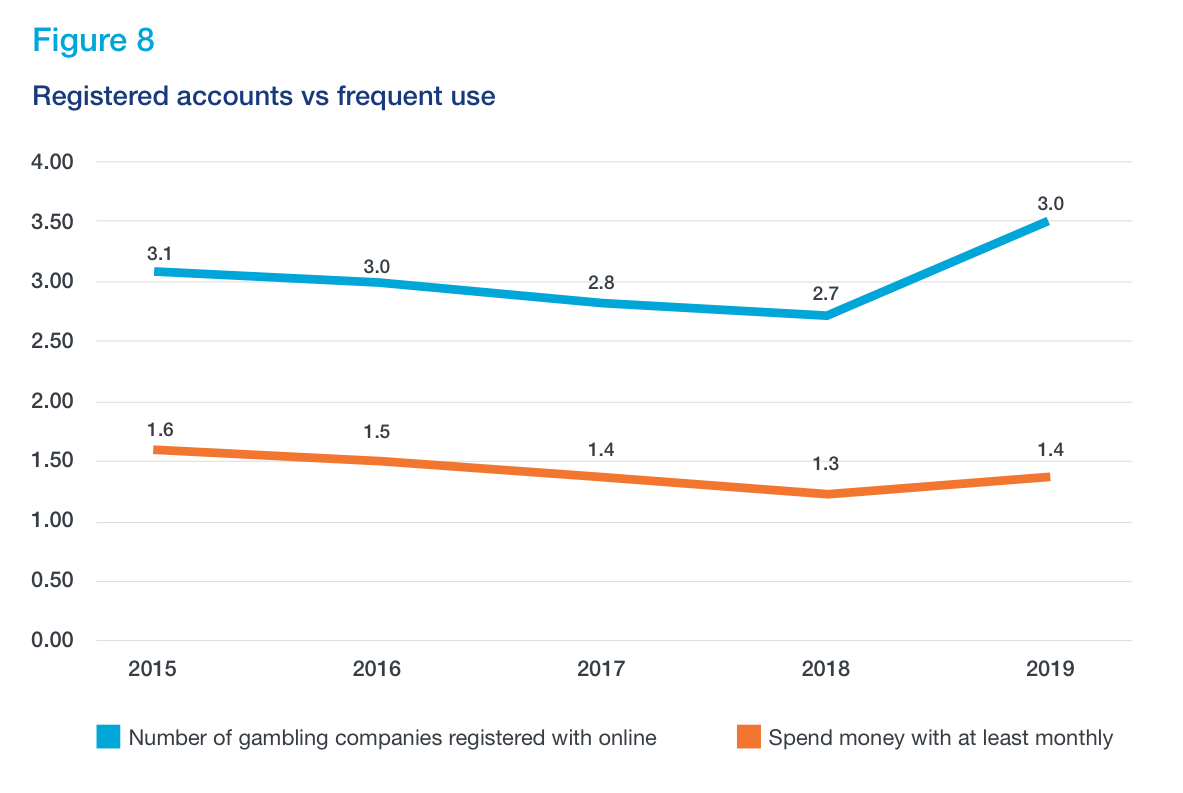
This issue is highlighted by data which shows 56% of online gamblers have more than one gambling account and on average they have 3 accounts as shown in Figure 8 17.
The following table shows the proportion of customers who play multiple activities and the equivalent prevalence of problem gambling for each of these groups 18.
Aged 16 and over with a valid DSM-IV or PGSI score
| Number of gambling activities | Combined GB Health Surveys 2016 | Health Survey England 2018 |
|---|---|---|
| 1 | 0.3% | 0.2% |
| 2-3 | 0.4% | 0.7% |
| 4-6 | 3.2% | 1.2% |
| 7 or more | 13.2% | 15.1% |
The implementation of multi-operator self- exclusion schemes and other gambling management tools which are player rather than operator centric have demonstrated how progress can be made. Supporting those who wish to limit or stop gambling is a regulatory focus. Our data shows 5% of adult gamblers in Great Britain (1.9 million) have ever excluded 19.
GC action
We are continuing to press the industry to use technology to create a single view of the consumer. We recognise the challenge of keeping a customer safe where operators currently only have a partial view of a customer’s behaviour. That is why we have bought together technology providers, data scientists, academics, researchers and financial service providers to work with us to develop solutions to provide a ‘single customer view’.
References
17 Online gamblers who hold one or more gambling accounts. Gambling participation in 2019 behaviour awareness and attitudes (opens in new tab)
18Gambling behaviour in Great Britain 2016and Health Survey for England 2018 supplementary analysis on gambling – December 2019 update (opens in new tab)
19Gambling participation in 2019 behaviour awareness and attitudes (opens in new tab)
The person gambling - Identification of at-risk behaviours and vulnerability Next section
Underage gambling
Last updated: 27 May 2021
Show updates to this content
No changes to show.
